Check Recent Access on Microsoft to Secure Your Account

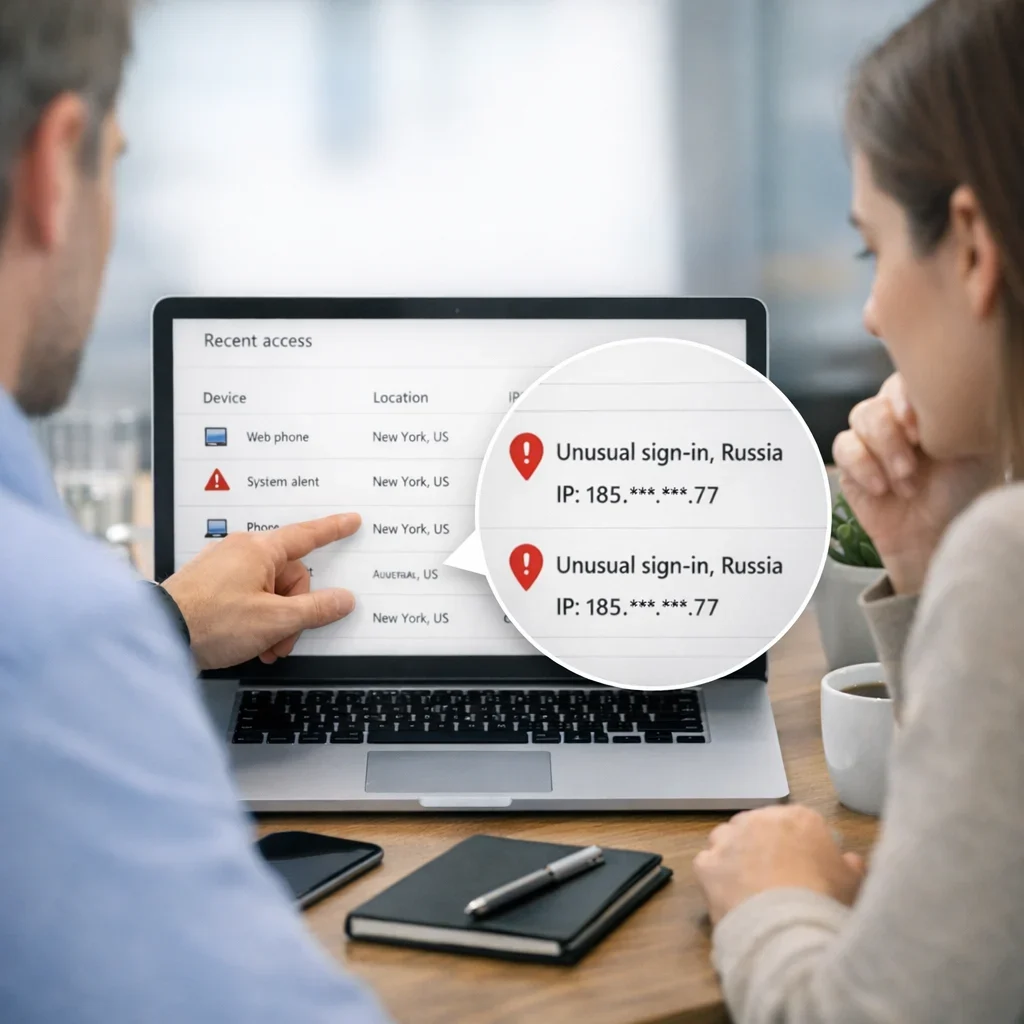
Imagine coming home after a long day at work only to find someone has been snooping on your computer. Recent Microsoft access logs are an effective way to check who has accessed your account and what they have been doing. Whether you need this for work, to protect your privacy at home, or just to ensure that no one is sneaking into your account at the gym, here’s how to do it.
Why is it important to review recent access?
Reviewing recent access on Microsoft isn't just a paranoid whim. It's an essential security measure to protect your data. In a world where information is the new gold, knowing who has access to your account can save you from a lot of headaches. If you work from home, for example, it's crucial to ensure that no coworker is sneaking into your account to look at those “sensitive” files you keep under lock and key.
How to access recent access information
Microsoft has a fairly intuitive system for you to check who has accessed your account. Here are the steps to follow:
- Log in to your Microsoft account.
- Go to the Security section.
- Click on Recent Activity.
- Review the list of accesses and check for anything suspicious.
If you see access from an unrecognized location, alert! It's time to take action.
Common mistakes when reviewing recent access
- Not reviewing accesses periodically; security is not a one-time affair.
- Ignoring alerts of access from unknown locations.
- Not changing the password after detecting suspicious accesses.
- Assuming that if you haven't noticed anything strange, everything is fine.
Quick tips to protect your account
- Change your password regularly, at least every three months.
- Enable two-step verification for an extra layer of security.
- Review your connected devices and disconnect those you don't use.
- Set up alerts for suspicious activity on your account.
What to do if you detect unauthorized access?
If, after reviewing recent accesses, you find something unusual, follow these steps:
- Change your password immediately.
- Review your account's security settings.
- Check the activity history to identify what information was accessed.
- If necessary, change your security questions and enable two-step verification.
Quick reference table on recent access
| Access Type | Recommended Frequency | Actions to Take |
|---|---|---|
| Account access from a new device | Immediate | Change password, enable notifications |
| Access from an unusual location | Monthly | Verify activity, review security settings |
| Regular access from a known device | Quarterly | Confirm no changes in security |
Tips for effective recent access review
Reviewing recent accesses doesn’t have to be a tedious task. Here are some practical tips to make this review a more efficient and less painful process:
- Set a fixed schedule: Dedicate a few minutes each week or month to review accesses. If you do it routinely, it will become a habit and won't take much time.
- Use filters: If you have many accesses, use filters to view only accesses from a specific period or device. This will help you focus on what really matters.
- Document your findings: Keep a record of any unusual access. Note the date, time, and any relevant details. This can be useful if you need to report suspicious activity later.
- Share the responsibility: If you work in a team, ensure everyone is aware of the importance of reviewing accesses. A couple of extra eyes always help to catch what one might overlook.
Examples of suspicious accesses and how to act
Identifying suspicious accesses can be tricky if you don't know what to look for. Here are some concrete examples and the actions you should take:
| Scenario | Description | Recommended Actions |
|---|---|---|
| Access from an unknown country | Your account shows access from a country you have never visited. | Change password, enable two-step verification, review recent activity. |
| Access outside of normal hours | Access to your account is recorded in the middle of the night. | Investigate the device used, change password, consider temporarily disabling the account. |
| Unrecognized device | Access has been made from a device you have not used before. | Disconnect the device, change password, review security settings. |
If any of these situations arise, don't take it lightly. Acting quickly can make the difference between a secure account and a digital disaster.
The importance of continuous education
Digital security is not a topic to be taken lightly. Technology is advancing rapidly, and so are the tactics of intruders. Therefore, staying informed is key. Here are some ways to keep learning:
- Webinars and online courses: Many platforms offer courses on cybersecurity. Investing a couple of hours a month can give you valuable tools.
- Blogs and podcasts: Follow cybersecurity experts who share tips and industry news. Listening to their experiences can open your eyes to new threats.
- Discussion groups: Join forums or social media groups where digital security is discussed. Sharing experiences with others can enrich your knowledge.
Remember, security is an ongoing process. It’s not just about reacting when something goes wrong, but anticipating problems. So, let’s review those recent accesses and keep your account safe!
What if I told you that you can do more than just review accesses?
Reviewing recent accesses is just the tip of the iceberg. Protecting your Microsoft account involves a series of proactive actions that go beyond checking the history. Here are some strategies that will not only help you identify intruders but also prevent them from reaching your digital doorstep in the first place.
1. Use strong and unique passwords
How many times have you heard that a secure password is the first line of defense? It’s not just a cliché. A strong password is like a good lock on your door. So, let’s get to work!
- Combine uppercase and lowercase letters, numbers, and symbols.
- Avoid using personal information, such as your name or birthdate.
- Consider using a password manager to generate and store complex passwords.
2. Keep your software updated
Software updates aren't just for making your device look nicer. Many of them fix security vulnerabilities. So, if you see that update notification, don’t ignore it. Here are a couple of tips:
- Set your device to update automatically.
- Periodically check for pending updates in your Microsoft applications.
3. Educate your circle
Digital security is not just one person's responsibility. If you share your account with family or coworkers, make sure everyone is on the same page. Here are some ways to do this:
- Conduct short training sessions on digital security.
- Share useful articles or resources on how to identify suspicious emails or malicious links.
- Encourage a culture of security: make everyone feel responsible for protecting information.
The dark side of the cloud: What about third-party accesses?
In the digital age, it’s common to connect your Microsoft account with third-party applications. While this can be useful, it can also open the door to unnecessary risks. Here are some guidelines for managing these accesses:
- Review connected applications: Regularly check your account settings and verify which applications have access to your information. If there’s one you no longer use, disconnect it!
- Limit permissions: Ensure that applications only have access to what they really need. Not all data is necessary for an app to function.
- Be wary of unknown applications: If an app asks to access your Microsoft account, do a little research before giving it the green light. Look for reviews and check its reputation.
Example of reviewing third-party accesses
Imagine you’ve connected your Microsoft account to a task management app. After a while, you decide you no longer need it. Here’s how to disconnect it:
- Log in to your Microsoft account.
- Go to the Security section.
- Look for the Connected Apps and Services option.
- Find the app in the list and select Disconnect.
It's that easy. A small step can be a big leap in protecting your information.
The mindset of a digital detective
Finally, adopting the mindset of a detective can change the game. Don’t just be a passive observer; become an investigator of your own security. Here are some tips to cultivate that mindset:
- Ask questions: If something doesn’t add up in your recent accesses, investigate. Who is that device? Why are there accesses at strange hours?
- Develop a critical approach: Not everything that glitters is gold. Be suspicious of emails or messages that seem too good to be true.
- Act immediately: If you see something suspicious, don’t wait until tomorrow. Quick action can be key to avoiding bigger problems.
At the end of the day, digital security is a constant effort. It’s not just about reacting, but about anticipating. So, let’s review, disconnect, and protect ourselves!
Frequently asked questions about recent access on Microsoft
What information is displayed in the recent access section?
In the recent access section, you can see the date and time of each access, the approximate location, and the device used. This information is crucial for detecting any suspicious activity.
Can I disable the option to show recent accesses?
It is not advisable to disable this option, as it is a useful tool for protecting your account. However, you can adjust your notification preferences to be informed about unusual accesses.
What should I do if I forget to change my password after detecting suspicious accesses?
Don't worry, even if you haven't changed the password immediately, do it as soon as possible. It is also advisable to review your security settings and enable two-step verification.
Is it safe to save my password in the browser?
Saving your passwords in the browser can be convenient, but it’s not always the safest option. If you choose to do so, make sure your device is protected with a strong and updated password.
Where can I find more information about online security?
You can check useful resources such as those provided by INCIBE, where you will find guides on how to protect your information online.
Updated on 04/03/2026. Content reviewed using experience, authority and trustworthiness criteria (E-E-A-T).
You can support the project or share this article in one click. At least this block does something useful.